- Community Home
- Announcements
- SIM Swap Fraud: 2 factor-authentication
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Subscribe
- Mute
- Printer Friendly Page
SIM Swap Fraud: 2 factor-authentication
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 10:16 AM - edited 07-14-2021 10:18 AM
Hey Community,
We’re pleased to announce that as of July 14, 2021, SIM card changes have been re-enabled in My Account.
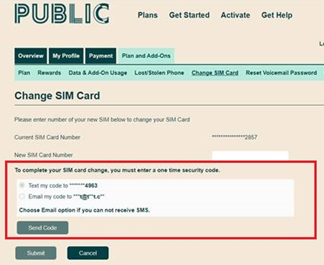
We have now implemented an additional step in the form of a 2 factor-authentication code to secure this process. This code can be sent via SMS or email, and must be verified to complete the SIM swap.
For more details, please see below.
All the information below can be found in this Help Article.
What is SIM swap fraud?
Efforts by fraudsters to gain unauthorized access to customer accounts with the goal of accessing banking information is on the rise. As part of our commitment to protect our customers’ personal information, we have robust security protocols in place that are designed to protect the privacy and security of our customers.
SIM swap fraud, or SIM jacking, is a type of fraud that occurs when fraudsters gain access to your Self Serve account, to replace your SIM card information with their own. After replacing your SIM card, all communications will be redirected to the fraudster’s device. They will then be able to intercept recovery SMS/calls, and gain access to your personal banking, ecommerce, email and social media accounts.
How does SIM swap fraud happen?
Fraudsters can obtain customer Self Serve account credentials through malware, phishing attempts or data breaches on websites where login credentials are the same as your Self Serve account.
How do I know if I’ve been targeted by a SIM swap fraud?
You may have been a target of SIM swap fraud if you have suddenly lost service for no apparent reason. If this is the case, please follow the below steps to confirm your SIM card information has not changed.
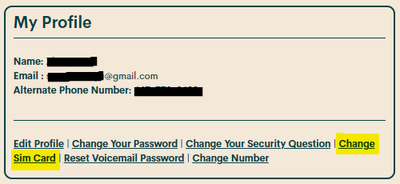
- Log in to your Self Serve account
- Select “Change SIM card” from the main page
- Confirm that the last four digits of the SIM card in Self Serve match the one in your device. If the digits do not match, you may have been targeted by a SIM swap fraud.
What do I do if I’ve been targeted by SIM swap fraud?
If you have been targeted by SIM swap fraud, we recommend you take the following actions to secure your account:
- Change your Self-Serve account password and security question immediately to lock the fraudster out of your account
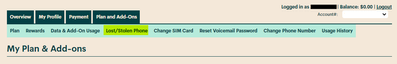
- Put your phone into Lost/Stolen mode to suspend the fraudster’s service, to do this follow the below steps:
- Log in to you Self-Serve account
- Go to Plans and Add-Ons, then select “lost/stolen phone”
- Select “suspend service”
- Then, submit a ticket here - our Moderator team will be able to restore your original SIM card.
- We also recommend contacting your financial institutions to ensure your banking and credit card accounts have not been accessed, and checking your social media accounts for any suspicious activity. Make sure you change your passwords to these accounts immediately.
- You may also want to report the fraud to your local police and the Canadian Anti-Fraud Centre at 1-888-495-8501, as well as contact the two national credit bureaus to request a copy of your credit reports and place a fraud warning on your file (Equifax Canada Toll free:1-800-465-7166 and TransUnion Canada Toll free: 1-877-525-3823).
How to protect against SIM swap fraud?
Given the increase the telecommunications industry has seen in fraudulent activity like SIM swaps and unauthorized porting, we recommend that Canadians take the following steps to protect themselves:
- Protect your information: limit the amount of personal information about you online; fraudsters can use this information to verify your identity when attempting to swap your SIM. Be careful to not click on phishing emails (and texts) that ask you to provide and/or validate private information.
- Guard your phone number: don’t add your phone number to any online accounts where it is not necessary. The fewer accounts you have associated with your number, the lesser your risk.
- Use strong and unique passwords for each of your accounts: using the same password across multiple accounts is a hacker’s jackpot. When you use the same password across different accounts, remember that once they successfully hack one account, they’ve hacked them all. We also recommend that you change your passwords, including your Self-Serve password regularly.
- Set up authentication methods that aren’t text based: often, online accounts will require you to set up two-factor-authentication (2FA) for added protection; with 2FA, you need to authenticate yourself with something in addition to your username and password, such as a code that is sent to your device by text. With SIM swap fraud on the rise, you may want to use something other than your phone number for 2FA like an authenticator app or security key.
While Public Mobile is actively working on ways to help keep our customers safe, please make sure to stay vigilant, and be aware of any suspicious activity.
- The Public Mobile Team
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 01:37 PM
Great to see that the option for self-serve SIM Swap is back... particularly for @darlicious's significant other who seems to go through a new SIM every month! 😂
In terms of security, I agree that time will tell whether this is an effective solution or not. It's a great step in the right direction, and the added challenge will definitely make things more secure. How secure it really is will all depend... if somebody really wants access to your account/SIM/whatever, there are many ways of doing it through any variety of ways, social engineering, technical espionage, or however else.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 12:42 PM - edited 07-14-2021 01:35 PM
I agree with @Anonymous
We seen before that people got simjacked and unable to logon to My Account. So, either their My Account was compromised first or the email was first compromised and then My Account.
But of course, many people requiring SIM swap because they lost their phone or the old SIM was broken and hence they were unable to receive the SMS and an alternate way is needed, sadly in this case, email....
Let's see how it goes and hope for the best.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 12:37 PM
Great news Jade!!! Glad to have this feature back and will help the members so much!
* I am happy to help, but I am not a Customer Support Agent please do not include any personal info in a message to me. Click HERE to create a trouble ticket through SIMon the Chatbot *
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 12:28 PM
Thanks to PM for adding this balance between customer convenience and security.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 12:26 PM - edited 07-14-2021 12:31 PM
@hTideGnow wrote:
but one observation, masking out the phone number and email at the SIM request is not useful. When you are able to access My Account for SIM change, you can access the phone number and email there without trouble. So, there is no added security with the mask
This is insightful. Simply that masking is pointless here. I still think the 4 digit PIN would have been a better solution. But at least we have something more self-serve, not needing the mods.
The weak point is still the email. Someone could have already hacked your email. The not so weak point is whether someone has stolen the phone with the SIM in it and wants to take control of the account or port out afterwards.
Come to think of it...no I don't like this solution. But again...it's more self-serve now. I guess we'll see how often SIM-jacking and port-outs will occur.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 12:11 PM
A suggestion for PM to Consider
When a user changes his SIM, PM should automatically and immediately send the user an SMS as well as an email that your SIM card number has been changed. There is a good chance that the user will get one of the two — either the SMS or the email — and be alarmed in time to initiate actions that you suggest.
The banks, the email providers like Gmail etc, already do this when a user changes the password or other critical account changes.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 12:06 PM - edited 07-14-2021 12:06 PM
Best is that user can now check their SIM number (last 4 digits) again
but one observation, masking out the phone number and email at the SIM request is not useful. When you are able to access My Account for SIM change, you can access the phone number and email there without trouble. So, there is no added security with the mask
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 11:24 AM
Fantastic, that we are being kept up to date. This helps us when we refer a friend and allows us to provide our friend with up to date assistance, if needed.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 10:54 AM - edited 07-14-2021 12:46 PM
Nice work. Edit: (with reservations see further post)
(thank you for the bravo Jade_S) I'll reserve full acceptance until we see about any other fraudulent account activity.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 10:45 AM
@J_PM Thank you very much for improving the system and make it safer for our Community!😊
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 10:45 AM
Very good news! Thank you!
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 10:34 AM - edited 07-14-2021 10:34 AM
nice move to introduce 2FA
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
07-14-2021 10:23 AM
Nice work Public mobile.
This will be helpful and more convenient for customers.
- « Previous
-
- 1
- 2
- Next »