- Community Home
- Get Support
- Re: Sim swapping threat mitigation?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Subscribe
- Mute
- Printer Friendly Page
Sim swapping threat mitigation?
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-09-2019 05:12 PM - edited 01-05-2022 09:41 AM
I've been reading about SIM swapping, a current scam in which a smooth talker reports your cellphone as lost or stolen, and then convinces the cell company's employee that he or she needs a new SIM card. As soon as they activate your SIM in their phone they take over your cellphone account and begin impersonating you, with devastating results in most cases. It's a real problem that's happening more and more frequently and I think everyone should ask what steps are being taken at public mobile to help detect and prevent this kind of fraud. So ya, hey P Mobile folks, what's up with SIM swapping and how can your employees be trained to detect and prevent this from hapoenign to your loyal customers? Thanks for your help!
- Labels:
-
Service
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-24-2020 08:12 PM
Oh Boy, This threat is real, Not just cost money but can lead to Identity theft.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-28-2019 01:11 PM
@geopublic wrote:
@Iggyhart wrote:Has there been any updates on this as far as Public Mobile offering more security here? It seems requiring a port protection password would stop this in its tracks.
@Iggyhart The only way I see this happening is if providers are forced to implement it by legislation. Calling your MP maybe not a bad idea at this point.
Do any of the Canadian providers offer port protection? Maybe the articles I'd read saying that most carriers offer this are based in the USA.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-28-2019 12:43 PM
@Iggyhart wrote:Has there been any updates on this as far as Public Mobile offering more security here? It seems requiring a port protection password would stop this in its tracks.
@Iggyhart The only way I see this happening is if providers are forced to implement it by legislation. Calling your MP maybe not a bad idea at this point.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
12-28-2019 12:31 PM
Has there been any updates on this as far as Public Mobile offering more security here? It seems requiring a port protection password would stop this in its tracks.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-29-2019 03:48 PM
thx for the info, very helpful. part of my question was about what steps P. mobile was doing to keep on top of what is a fast evolving problem for all cell providers. I'll look inot this more closely now and if I have any useful input I'll get back to the community with it. thanks all...
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-09-2019 08:26 PM - edited 11-09-2019 08:51 PM
@joel_lisSim jacking is not isolated to Public Mobile. It is an issue that requires industry wide protocol change. You have to understand people demand things when it coming to porting, it has to be seamless, easy, quick. Currently the process is mostly automated with problematic ones throwing exceptions that require human intervention. There are minimal standard times defined by the CWTA tradegroup with supervision from CRTC that Public Mobile has to meet. Any changes will change all that and require rewrites. % wise SIMjacking is really a small phenomenon.
Public Mobile staff, I think is shielded by the extra long moderator time. It cuts both ways, it takes longer for people to social engineer (people might just go for an easier target).. but sucks for the victim (the thief got away, while victim waits). Currently Public Mobile sends a heads up text to the user of any port out attempt.
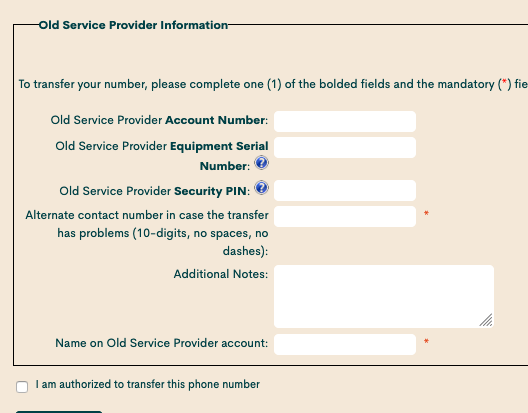
To port a wireless line, you need: Your Name, Phone number + (combination of: Account #, PIN or IMEI) So remember your attacker will need the information ahead of time. The first 2 is rather easy. IMEI can be had easier if you use an Android phone with a bad app. However all the information can be had really easily if you had been compromised by a RAT.
From my observation and experience, working in litigation and security (I see them once every other week, thankfully only from staff's personal devices). Nearly SIM jacking victims had been scooped ahead of time. The attacker knows the value of the target. Often the phone and/or the computer had been compromised.
Here is a few suggestions from my experiences (the objective is to minimize the risk of the information required to port is leaked out and damage mitigation):
1. Minimize your exposure to loosing your phone# ie don't use your wireless phone # as a 2FA method. Even VOIP services like textnow is more secure because it takes days, weeks to transfer a number out.
2. Be very particular with what kind of services you use (eg Bitcoin exchanges, might want to use another wireless# if you so inclined)
3. Be even more particular on what apps you install on your phone, especially if you use an Android phone. It doens't take much for your IMEI number to be betrayed. Oh don't rely on antivirus on Android because once they tracked something is amiss, your information will had been exfiltrated.
4. If you use Android phones use only reputable ones, or at the minimum use Android One Or pure Android. Avoid "Skinned" ones. Especially low cost Chinese phones, they have undocumented APIs which will betrayed you. That's their business models if they survive long enough, or someone will exploit that knowledge once they had folded.
5. Make sure your internet accessing devices are clean and patched. It wont' hurt to restore from a known good backup once a while.
6. This might be controversial but block all texts from unknown numbers. Also make sure people you know don't use unkown numbers. If they do, get them on Slack etc etc.
7. Since Public Mobile doesn't do hard credit check, modify the name in your account. It won't affect your credit card / autopay/ 1 times payment. Unless your account access has been compromised, it gives an added of protection.
8. Have a backup plan. If you are really paranoid, get an extra phone line on the Rogers network. Create a checklist of who to talk to / contact in case you got compromised. Also practice the checklist a couple of times and update it annually.
Other readers suggestions of not reusing passwords, password managers etc are great and should be practiced as part of good internet hygiene. At my work we use Google Titan keys for 2FA for anyone that needs computer access from receptionists to head of the company, they work great and I highly recommend them as the 2FA source. Yubikey is another good 2FA provider.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-09-2019 06:28 PM
@joel_lis To protect from sim jacking the most important link that needs to be protected is your email. Once your email is compromised it's pretty easy to do.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-09-2019 05:46 PM
The first protection is your password.
If someone hack into your password and login to your account, the hacker can change the SIM card for your account.
If a hack want to smooth talk a moderator to get access to your account, moderator will ask the folllowing to make sure that you are the owner of your account.
1. Ask you to login to your account
2. Ask you for your PIN number or
3. If you cannot provide PIN number, you will be asked to provide any 3 of the following:
- Complete mailing address,
- Email address,
- Alternate phone number,
- Date of birth,
- Last top up date & amount
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-09-2019 05:17 PM
@joel_lis wrote:I've been reading about SIM swapping, a current scam in which a smooth talker reports your cellphone as lost or stolen, and then convinces the cell company's employee that he or she needs a new SIM card. As soon as they activate your SIM in their phone they take over your cellphone account and begin impersonating you, with devastating results in most cases. It's a real problem that's happening more and more frequently and I think everyone should ask what steps are being taken at public mobile to help detect and prevent this kind of fraud. So ya, hey P Mobile folks, what's up with SIM swapping and how can your employees be trained to detect and prevent this from hapoenign to your loyal customers? Thanks for your help!
There is also the verification process here that needs to be completed before mods will do anything to your account.
* I am happy to help, but I am not a Customer Support Agent please do not include any personal info in a message to me. Click HERE to create a trouble ticket through SIMon the Chatbot *
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-09-2019 05:16 PM
As long as you're taking normal privacy protections, not reusing the same password, using secure passwords, only using private deices to login - etc. I would not worry about this too much.
Another way you may be able to protect yourself further is to use an e-mail alias, if someone you know is trying to impersonate you using your information, they may have your e-mail address. If you use an alias only for Public Mobile, that would be a way to mitigate that type of attack.
- Mark as New
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
11-09-2019 05:13 PM - edited 11-09-2019 05:14 PM
@joel_lis just don't give anyone your password or any info about your account. Many times, customers post info about their accounts and the account can get stolen.
